Privacy Policy
Kakao Healthcare Corp.(hereinafter referred to as “the Company”) collects, uses, and provides personal information based on the user’s consent, actively guarantees the user’s rights (right to self-determination of personal information), and complies with the personal information protection regulations and guidelines in Korea. Through this Privacy Policy, we will inform you of the purpose and method of using employee personal information and the measures taken to protect personal information. This Privacy Policy applies to users (hereinafter referred to as “Users”) who wish to apply for a job or use the affiliate proposal service of the Company.
- Personal Information Items and Purposes of Processing
* The Company collects and processes the minimum amount of personal information required for the purpose.
1) Recruitment (Job Application)
[When registering as an applicant]
o Purpose
– Identify and register the applicant
– Confirm the applicant’s intention to apply and proceed with the hiring process
– Provide guidance and notices for the hiring process
– Respond to inquiries
– Register the applicant in the talent pool (database) for the purpose of regular hiring (priority review of the applicant’s suitability for other hiring opportunities of the company)
o Required Items
– Name, contact information, email, application route
o Optional Items
– Resume and other non-structured information that the applicant directly enters or uploads through attachments, including information that may identify the individual
[When calculating compensation]
o Purpose
– Discussion of compensation calculation
o Required Items
– Proof of compensation calculation
[When finally selected]
o Purpose
– Confirmation of the identity of the employee, personnel management, conclusion/performance of labor contract (personnel placement, welfare benefits, education and training, salary contract, etc.), and use for creating a list of employees and payroll.
o Required Items
– (desired) Intranet ID, nationality, address, resident registration number (foreign registration number for foreigners)
o Optional Items
– Veterans’ affairs number
2) Affiliate Proposal
o Purpose
– Receipt and reply of affiliate proposals
o Required Items
– Name, phone number, email address
o Optional Items
– Personal identification information available in the affiliate proposal content
* The Company collects employee personal information through the user’s input method, and in some cases, through paper documents or emails in printed form.
- Processing and Retention Period of Personal Information
The company processes the user’s personal information only during the period necessary to achieve the purpose, and once the purpose is achieved, the user’s personal information is promptly destroyed. However, in the following cases, it is stored and destroyed separately:
1) The application history information of job applicants is kept for one year from the date of withdrawal for the purpose of confirming the application history and restricting re-application of unsuccessful interviewees. (However, the original value is safely converted so that it cannot be identified, and only used in the form of a comparative value.)
2) Information related to finally selected candidates that is allowed to be retained by relevant laws and regulations is stored for the period specified by the law. (However, if separate consent is obtained, personal information may be processed and retained within the purpose and period of use agreed upon.)
o For the purpose of issuing certificates of employment, including proof of employment history, of retired employees.
– Retention basis: Labor Standards Act
– Retention period: 3 years
o For the purpose of year-end tax settlement processing.
– Retention basis: Income Tax Act, National Tax Basic Act
– Retention period: 5 years
3) Reports to the Cyber Ethics Department and proposals for partnership are stored for 3 months after review of the relevant matters, and the information is promptly destroyed thereafter.
- Personal Information Processing Outsourcing
The company entrusts some of the necessary tasks for providing various services to users to external companies to process personal information. And it manages and supervises the entrusted subcontractors to ensure that they do not violate the personal information protection-related laws and regulations.
o Subcontractor: Ninehire Corp.
o Outsourced task: Provision and operation of recruitment management services.
- Provision of Personal Information to Third Parties
The company does not provide the personal information of users to third parties without their consent under the law, except in the following cases:
1) When the user has given prior consent under the law
2) When required by other laws and regulations
Occasionally, the company may offer a job opportunity to an applicant at a company (subsidiary, affiliated company, etc.) that has a special relationship with the company, but in this case, the company must contact the applicant in advance and go through the consent procedure before providing the job application to the relevant company.
- Personal Information Destruction Procedure and Method
The company promises to destroy the personal information of users promptly after the purpose of processing personal information has been achieved.
However, the company moves the information entered by the applicant for job application, etc. to a separate storage space that is distinguished from the original storage space after the purpose is achieved, and stores it for a certain period of time in accordance with internal guidelines (refer to 2. Handling and Retention Period of Personal Information) and other relevant laws and regulations before destruction. Personal information stored separately will never be used for any other purpose unless required by law.
When the retention period is over, the company uses technically irreversible methods to completely delete the information, and the personal information recorded and stored on paper documents will be crushed or burned for destruction.
- Rights, Obligations, and Method of Exercising them for Users
Users may request to view, modify, delete, or suspend the processing of their personal information at any time. However, for the smooth progress of recruitment, applicants cannot modify or delete their submitted applications after passing the document screening. If you wish to delete your personal information, please contact the recruitment department and we will promptly take action.
Contact information for the recruitment department: khc_recurit@kakaohealthcare.com
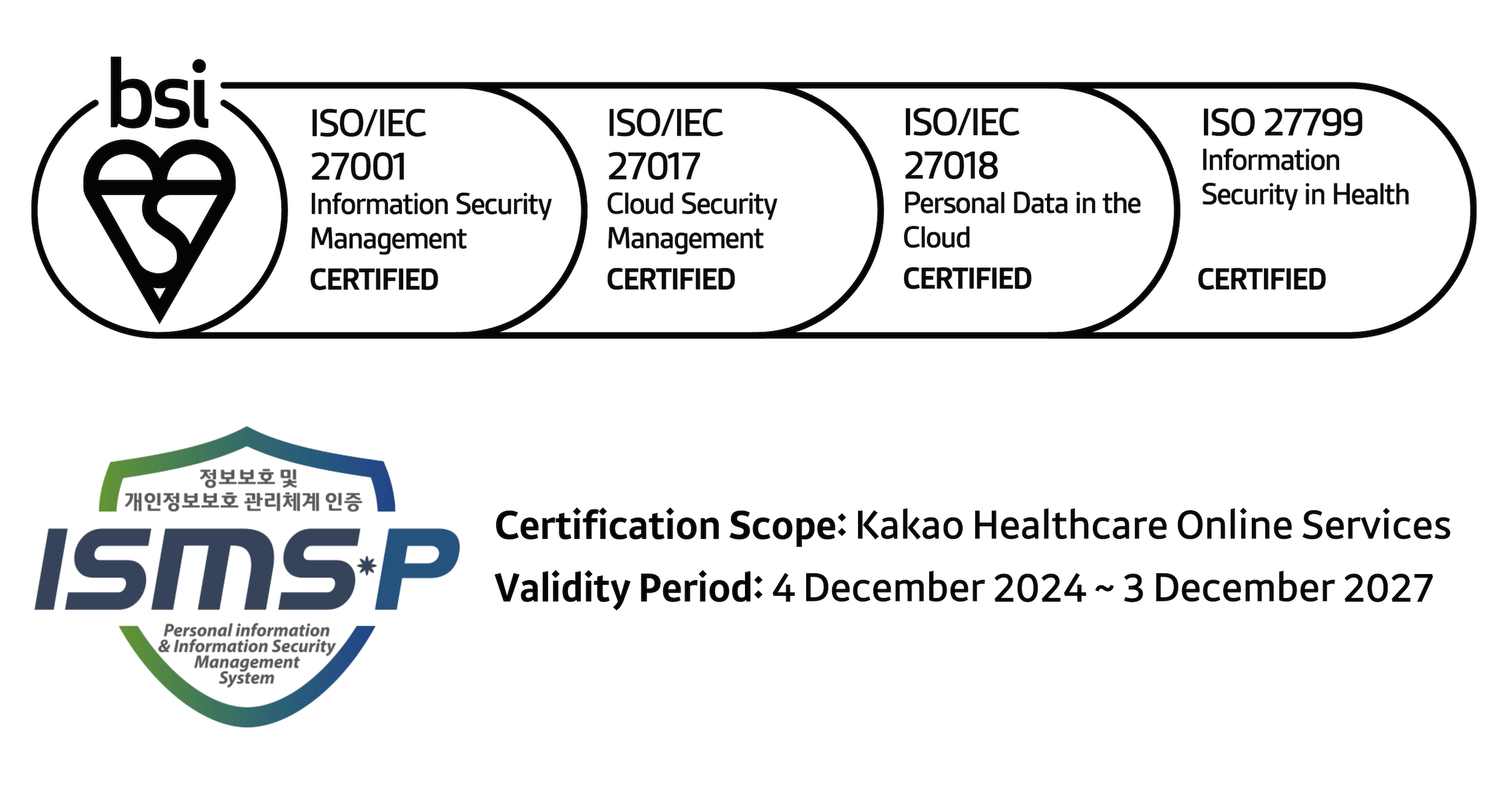
- Measures for Ensuring the Security of Personal Information
The company regards the user’s personal information as the most valuable asset and strives to take the following measures when processing personal information:
1) Encryption of user’s personal information: The company encrypts the user’s personal information during transmission using an encrypted communication channel and stores important information such as passwords in encrypted form.
2) Efforts to protect against hacking or computer viruses: The company installs systems in controlled areas to prevent the leakage or damage of user’s personal information due to hacking or computer viruses. We install systems that can detect and block intrusions by hackers and viruses 24 hours a day and install antivirus programs to prevent the system from being infected by the latest malicious code or viruses. In addition, we continue to research new hacking/security technologies and apply them to the service.
3) Minimizing access to valuable personal information: The company minimizes the number of employees who handle personal information and blocks external internet services from being used on work PCs to reduce the risk of personal information leakage. We establish systematic standards for creating and changing passwords for databases and systems that store and process personal information and conduct continuous audits.
4) Regular education for employees on protecting user’s personal information: We conduct regular education and campaigns on the obligations and security of personal information protection for all employees who handle personal information.
- Information on the Installation/Operation and Refusal of Automatic Collection Devices for Personal Information
We use and operate cookies, and users have the option to refuse them. Cookies are used to support faster and more convenient website usage and to provide customized services to users.
1) What are cookies?
Cookies are very small text files that a server used for operating a website sends to the user’s browser and are stored on the user’s computer.
2) Why are cookies used?
Cookies are used to store user preferences and settings, support faster web browsing, and improve services for convenience. This allows users to use the service more easily.
3) How can users refuse the collection of cookies?
Users have the right to choose whether to allow cookies or not. Therefore, users can choose to allow all cookies, have each cookie checked when it is saved, or refuse the storage of all cookies by setting options in their web browser. However, refusing cookie installation may make web usage inconvenient and may make it difficult to use some services that require login.
o Example of settings:
– For Internet Explorer: Tools menu at the top of the web browser > Internet Options > Privacy > Settings
– For Chrome: Settings menu on the right side of the web browser > Show Advanced Settings at the bottom of the screen > Content Settings button under Privacy > Cookies.
- Chief Privacy Officer and Department in Charge
For inquiries, complaints, advice, or other matters related to personal information protection, please contact the Personal Information Protection Officer and the department in charge. We will listen to our employees’ voices and do our best to provide prompt and sufficient answers.
o Chief Privacy Officer:
– Name: Soo-Yong Shin
– Contact: privacy@kakaohealthcare.com
o Personnel Management Department:
– Department: People Team
– Contact: khc_recruit@kakaohealthcare.com
o Personal Information Protection Department:
– Department: Information Security Team
– Contact: security@kakaohealthcare.com
If your personal information has been infringed and you need to report or consult about it, you can contact the following organizations for help:
o Personal Information Infringement Report Center:
– Tel: 118 (no area code needed)
– Website: http://privacy.kisa.or.kr
o Cyber Investigation Department of the Supreme Prosecutors’ Office:
– Tel: 1301 (no area code needed)
– Email: cid@spo.go.kr
o Cyber Investigation Department of the National Police Agency:
– Tel: 182 (no area code needed)
– Website: https://ecrm.cyber.go.kr
- Other Additional Policies
If there are any additions, deletions, or modifications to the above contents, we will explain them to our employees in advance through the company’s intranet. However, if there are any significant changes to important contents related to our employees’ precious rights or obligations, we will notify them at least 30 days in advance.
Effective Date: April 25, 2023.